MCAI Innovation Vision: AI × Quantum × Blockchain Convergence — A Three-Clock Framework for Capital Allocation, Verification, and Fault-Tolerant Optionality
A MindCast Foresight Framework for Pricing Non-Synchronized Timelines Across the Converging Computational Stack
Executive Summary
Artificial intelligence (AI), quantum computing, and blockchain converge into a unified control architecture. AI drives prediction and action. Blockchain enforces verification and coordination. Quantum computing expands the boundary of solvable problems. Independent development produced isolated gains; convergence produces interaction effects across three non-synchronized clocks.
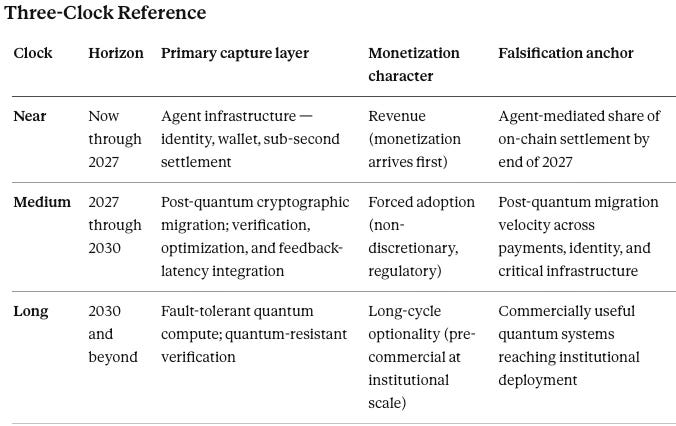
Mispricing occurs when capital treats agent infrastructure, post-quantum migration, and quantum compute as synchronized when revenue realization sits on three separate timelines.
Near-term capital formation concentrates on agent infrastructure and post-quantum cryptographic migration. Medium-term value accrues to firms owning verification layers, optimization pathways, and feedback-latency compression. Long-term dominance belongs to architectures that internalize the full stack as a single product surface rather than three separate procurements. Markets, governance, and infrastructure reorganize around machine-native execution. Incumbents adapt or lose control over coordination, security, and value capture.
Allocation Principle
Capital allocation across the stack must separate revenue, margin defense, and optionality into distinct bets aligned to each clock.
Pricing Error
Markets misprice convergence by bundling three timelines into a single narrative. Agent infrastructure generates near-term revenue. Post-quantum migration drives forced adoption on a regulatory clock. Quantum compute remains long-cycle optionality. Correct pricing separates these layers and assigns capital accordingly. Bundled pricing transfers alpha from investors to issuers who narrate convergence faster than they deliver it.
Governing Structure
The convergence thesis resolves into a control problem across decision, verification, and feasibility under non-synchronized timelines.
I. Structural Convergence: From Tools to System Architecture
Three technologies shift from standalone tools into interdependent system layers. AI generates decisions. Blockchain validates and executes those decisions. Quantum computing expands the solution space those decisions operate within. Integration creates a closed-loop system where decision, verification, and optimization reinforce each other, and feedback cycles accelerate as decision-to-execution latency collapses.
Power shifts toward entities that control integration — but only where the integration owns defensible assets. Integration without ownership produces no durable advantage.
Investor signal: Firms describing themselves as “integration layers” without proprietary data, network effects, or verification moats sell commodity orchestration at venture multiples.
II. Constraint Collapse: Intelligence, Trust, and Feasibility
Each domain removes a fundamental constraint. AI reduces uncertainty in decision-making. Blockchain eliminates reliance on centralized trust. Quantum computing breaks classical computational limits. Systems operate under equilibrium conditions where scale, speed, and autonomy reinforce each other.
Additive convergence delivers three separate gains on three separate timelines. Multiplicative convergence delivers interaction effects — AI verification improves when blockchain provides cryptographic attestation, and blockchain coordination improves when AI agents generate more sophisticated strategies. Interaction effects must produce measurable performance deltas — speed, cost, or accuracy — or the convergence thesis collapses into narrative bundling.
Competitive advantage migrates toward architectures that internalize all three capabilities on a deliberate timeline rather than chasing each domain separately.
III. Autonomous Systems: Machine-Native Coordination
Autonomous agents become the operational layer of the converged stack on non-overlapping commercialization timelines. AI agents interpret environments, generate strategies, and execute transactions today. Blockchain rails already enable machine-to-machine settlement without human intermediaries. Quantum-enhanced optimization remains pre-commercial at institutional scale — cryptographically relevant quantum systems are under active development, and fault-tolerant machines capable of solving institutional-scale optimization problems have not yet reached commercial deployment. Investors who conflate timelines overpay for quantum exposure and underprice agent infrastructure.
Revenue emerges where agents replace human coordination costs in high-frequency environments. Near-term capital formation concentrates on three capture points. AI agents with persistent identity, wallet control, and cross-protocol reach generate the first wave of machine-native revenue. Blockchain execution layers that settle agent transactions at sub-second latency capture the coordination spread. Post-quantum cryptographic migration — not quantum compute itself — becomes the first monetizable quantum-adjacent opportunity, because every blockchain network, financial rail, and identity system must transition before fault-tolerant quantum systems arrive.
Medium-term value accrues to firms treating Cognitive Digital Twin (CDT) architectures, agent orchestration, and quantum-resistant verification as a single product surface. Human oversight migrates from direct control to boundary setting and exception handling. Firms compressing the decision-to-execution loop capture disproportionate margin on coordination that human institutions previously mediated.
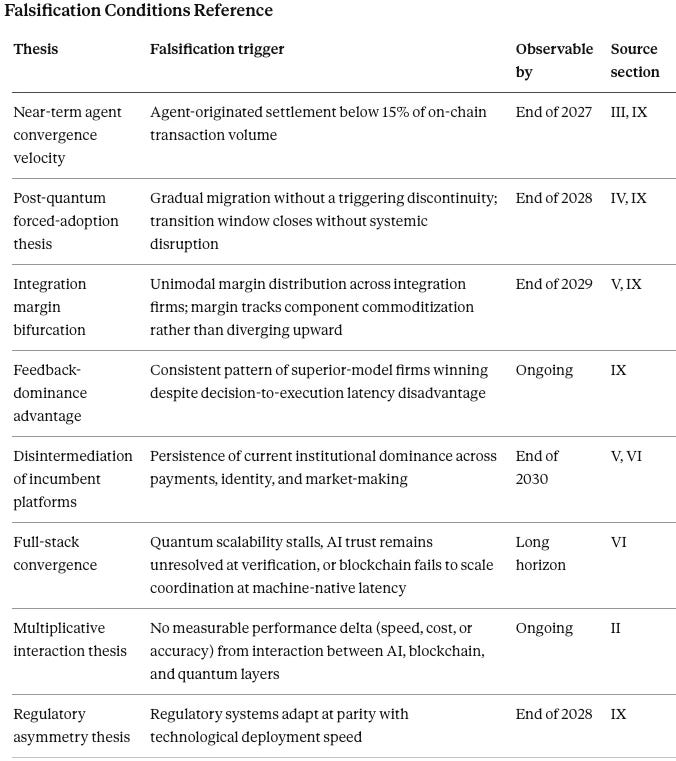
Falsification condition: Agent-mediated transaction volume, measured as a share of on-chain settlement, fails to cross a meaningful threshold by the end of 2027.
Contact mcai@mindcast-ai.com to partner with us on Predictive Law and Behavioral Economics + Game Theory Foresight Simulations. To deep dive on MindCast upload the URL of this publication into any LLM and prompt ‘reconstruct MindCast framework with three degrees of cited sub links.’ See Live-Fire Game Theory Simulators, Runtime Predictive Infrastructure.
IV. Security and Instability: Cryptographic Disruption and System Risk
Quantum computing threatens existing cryptographic systems that underpin digital trust. Blockchain networks, financial systems, and internet security protocols face obsolescence without transition to post-quantum standards. Every encrypted system in operation today carries latent breach risk under a quantum arrival scenario.
“Harvest now, decrypt later” attacks already accumulate encrypted data against the future arrival of cryptographically relevant quantum systems, and the attack window widens every year the transition lags. AI-generated outputs simultaneously increase information entropy, requiring stronger verification. System stability depends on synchronization between post-quantum cryptography, AI verification, and blockchain execution. Misalignment produces systemic risk.
Investor capture point: Post-quantum cryptographic migration is the most underpriced security transition in the converged stack. Spending is non-discretionary because failure equals catastrophic loss of trust. Firms delivering drop-in post-quantum primitives for blockchain consensus, identity, and payment rails operate in a market where the purchase decision is not whether but when. Regulatory forcing functions — National Institute of Standards and Technology post-quantum standards, central bank digital currency deployment, and critical infrastructure mandates — compress the wheninto a narrower window than most incumbents are prepared for.
Falsification condition: Post-quantum adoption proceeds on a timeline so gradual that the transition window closes without systemic disruption.
V. Control and Power: Reallocation Across the Stack
Control concentrates where the three layers are hardest to substitute. Margin concentrates where substitution risk approaches zero. Investors must distinguish defensible integration from commodity integration before allocating capital to the “integration layer” thesis.
A common error treats integration as inherently defensible. Integration layers become thin, substitutable, and disintermediable when they sit above commodity capabilities and own no underlying asset. A routing layer between three open protocols captures little durable margin. Defensible integration requires at least one of three conditions: proprietary data that improves the orchestrated system over time, network effects that make the integrated stack more valuable as usage grows, or regulatory and verification moats that third parties cannot replicate at reasonable cost.
Three categories of firm meet those conditions. First, firms owning the verification layer — the cryptographic, attestation, and post-quantum security primitives that every agent transaction depends on — capture a tax on coordination that scales with the stack. Second, firms owning optimization pathways — proprietary models, simulation architectures, and decision engines that outperform public alternatives on institutional problems — capture margin that thinner competitors cannot arbitrage away. Third, firms compressing feedback latency between decision, verification, and execution reduce the real-time cost of coordination below what incumbents can match.
Integration captures value only when it owns what others cannot replace. Integration without control becomes a cost center; integration with control becomes a tax on the system.
Incumbent platforms face disintermediation where decentralized and autonomous systems bypass traditional chokepoints in payments, identity, and market-making. Governments face a regulatory asymmetry — enforcement capacity lags deployment velocity, and regulation concentrates on the few visible integration points rather than the distributed stack.
Value destruction concentrates in intermediaries that coordinate without owning verification, optimization, or distribution.
Investor positioning test: A portfolio company claiming “integration layer” advantage must answer three questions on the record. What proprietary asset does the integration own? What happens to margin if each underlying layer becomes open and commoditized? How does feedback latency compare to the fastest vertically integrated competitor? Firms unable to answer all three are selling commodity orchestration at venture multiples.
Falsification condition: Margin compression at the integration layer tracks the commoditization curve of the underlying components rather than diverging upward.
VI. Forward Trajectory and Falsification Conditions
Convergence produces observable shifts that can be tracked and priced in real time.
Near horizon (now through 2027). Autonomous agents with persistent identity and transaction capability reduce human-mediated exchange in narrow, high-volume markets first — decentralized finance settlement, machine-to-machine data markets, and automated supply-chain coordination. Post-quantum cryptographic adoption accelerates across payment rails, identity systems, and blockchain consensus layers. Agent-mediated transaction share and post-quantum migration velocity serve as the two leading indicators.
Medium horizon (2027 through 2030). Integrated architectures consolidate around firms owning verification, optimization, and feedback-latency advantages simultaneously. Regulatory fragmentation produces jurisdictional arbitrage opportunities and jurisdictional risk in equal measure. Firms that compressed near-horizon capture into durable assets extend their lead; thinner integrators compress against commoditization.
Long horizon (2030 and beyond). Cryptographically relevant quantum systems reach institutional deployment. Firms owning quantum-resistant verification plus quantum-enhanced optimization pathways capture the final layer of the converged stack.
Consolidated falsification conditions. Full-stack convergence fails if quantum scalability stalls past the long-horizon window, AI trust remains unresolved at the verification layer, or blockchain fails to scale coordination efficiently at machine-native latency. Persistence of current institutional dominance across payments, identity, and market-making would falsify the disintermediation thesis. Integration-layer margin compression tracking component commoditization would falsify the control-reallocation thesis even if the technical convergence proceeds on schedule.
Failure to observe any of these invalidates core convergence assumptions and requires model recalibration rather than incremental adjustment.
VII. Opportunity by Actor Class
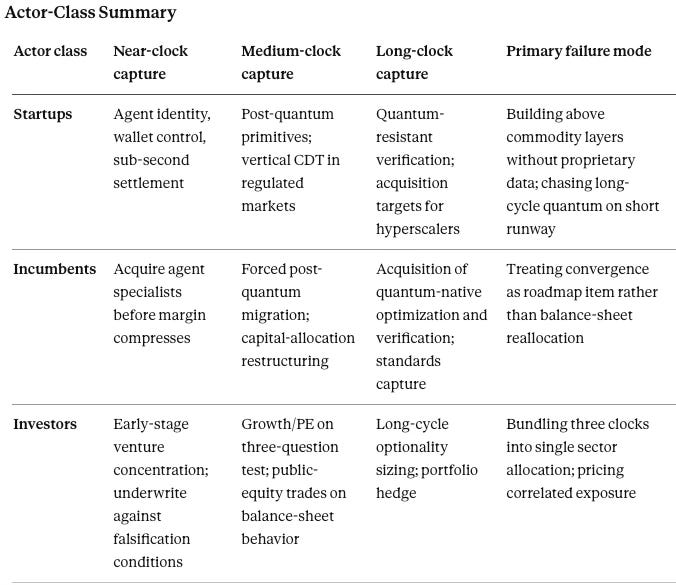
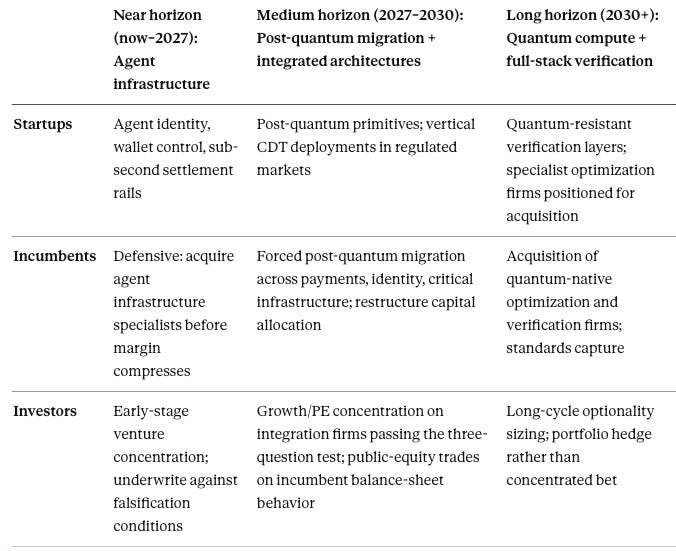
Convergence produces different games for different actors. Startups, incumbents, and investors face distinct capture points, distinct timelines, and distinct failure modes. Treating them as one audience collapses the allocation signal.
Startups
Startups win where regulatory tailwinds favor speed over scale and where defensible wedges do not require hyperscaler capital. Three entry points meet both conditions.
Post-quantum cryptographic primitives for blockchain consensus, identity, and payment rails offer the clearest startup wedge. The purchase decision is forced by regulatory timelines rather than budget discretion, and incumbents cannot match the focus of specialist teams shipping drop-in replacements. Speed to certified deployment beats balance-sheet scale.
AI agent infrastructure — persistent identity, wallet control, cross-protocol reach, and sub-second settlement — captures the coordination spread before incumbents rebuild their stacks. Startups that own the agent identity layer become the access point every downstream application routes through.
Vertical CDT deployments in regulated markets (litigation, antitrust, market structure, insurance) generate proprietary data that compounds defensibility over time. Horizontal CDT plays compete against hyperscaler foundation models; vertical deployments convert domain expertise into network-effect data moats that hyperscalers cannot replicate without the same regulatory access.
Startup failure modes. Building above commodity layers without proprietary data. Pricing on long-cycle quantum narrative while burning runway on short-cycle agent infrastructure. Pursuing horizontal orchestration when vertical ownership is available.
Incumbents
Incumbents face different disintermediation timelines depending on which chokepoint they own. The defensive playbook is not uniform.
Banks, payment networks, and identity providers face the most compressed timeline. Post-quantum migration is non-discretionary and arrives before agent settlement scales. Acquisition of specialist post-quantum teams beats in-house rebuild on both speed and talent density. Incumbents that wait for regulatory clarity lose the window.
Exchanges, market-makers, and clearinghouses face agent-settlement pressure next. The question is whether to build machine-native rails inside the existing venue or spin them out as separate infrastructure. Inside-the-venue builds preserve margin but carry cannibalization risk; spinouts capture the new pool but dilute the legacy franchise.
Cloud and infrastructure providers face verification-layer competition. Hyperscaler advantage erodes where verification primitives become the product rather than a feature. The defensive move is to own the attestation layer through acquisition or standards capture before it becomes a pricing bottleneck, not to compete on foundation models where margin compresses fastest.
Incumbent failure mode. Treating convergence as a product-roadmap item rather than a balance-sheet reallocation. Firms that fund convergence out of existing business-unit budgets lose to firms that restructure capital allocation around the three-clock framework.
Investors
Investor strategy depends on stage, liquidity horizon, and mandate. The three-clock framework implies a barbell rather than a single bet.
Early-stage venture. Concentrate on post-quantum primitives, agent identity and wallet infrastructure, and vertical CDT deployments. Timeline alignment matters more than sector breadth. Underwrite against the falsification conditions in Sections III through V; firms that cannot articulate which condition would kill their thesis are underpricing their own risk.
Growth-stage venture and private equity. Concentrate on integration firms that have already cleared the three-question positioning test — proprietary asset, commoditization resilience, feedback-latency advantage. Firms that pass all three command premium multiples defensibly; firms that pass fewer than three compress.
Public equities. Long positions on incumbents restructuring capital allocation around the three-clock framework; short or underweight positions on incumbents treating convergence as a roadmap item. The directional trade is on balance-sheet behavior, not on technology adoption.
Long-cycle capital (sovereign, pension, endowment). Hold quantum-compute optionality as a portfolio hedge rather than a concentrated bet. Institutional-scale quantum optimization remains pre-commercial and the payoff distribution is fat-tailed; sizing should reflect optionality value, not expected-value estimation.
Investor failure mode. Bundling the three clocks into a single sector allocation. A portfolio that treats “AI × quantum × blockchain” as one bucket overpays for correlated exposure and underprices the timing risk each layer carries individually.
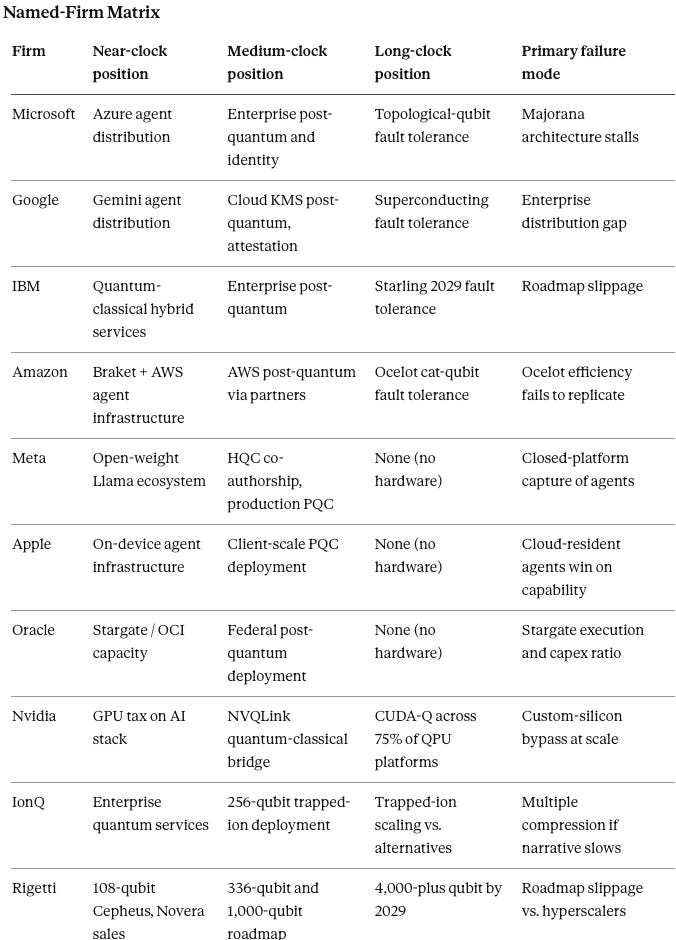
VIII. Opportunity Matrix: Clocks × Actors
The matrix below crosses the three commercialization clocks against the three actor classes. Each cell defines the primary capture point or failure mode for that combination.
Reading the matrix. Diagonals carry the cleanest capture logic — startups on the near horizon, incumbents on the medium horizon through forced migration, long-cycle capital on the long horizon. Off-diagonal positions carry execution risk: startups chasing long-horizon quantum burn runway; incumbents competing on near-horizon agent infrastructure face faster, more focused competitors; investors holding near-horizon positions past the medium-horizon consolidation watch margins compress.
IX. Foresight Simulation
High-Level Simulation Output
Convergence resolves into an interacting system spanning capital markets, technology infrastructure, institutional regulation, and market adoption. Each domain operates under distinct incentives, latency constraints, and adaptation capacities. A foresight simulation integrates Cybernetic Control (CC), Game Regime Identification (GRI), Strategic Game Theory (SGT), Field-Geometry Reasoning (FGR), Strategic Behavioral Coordination (SBC), Institutional Cognitive Plasticity (ICP), Installed Cognitive Grammar (ICG), and Causation Vision (CV) to generate forward predictions under constrained interaction.
Three dominant dynamics emerge from the simulation. Constraint geometry forces non-optional transitions, most visibly in post-quantum cryptographic migration. Institutional lag creates temporary arbitrage windows that close rapidly once constraint thresholds are crossed. Coordination failures concentrate where incentives across domains remain misaligned.
Current Domain State
The simulation classifies each domain by four states: Arena, Labyrinth, Fog, and Trap. Arena denotes open experimentation with narrative expansion and mispricing risk. Labyrinth denotes rising constraint density where integration complexity blocks naive entry. Fog denotes delayed response under high uncertainty with reactive rather than anticipatory action. Trap denotes deterministic local outcomes where exit becomes costly once entered.
Capital markets currently occupy Arena — early experimentation, narrative expansion, mispricing risk active. Technology infrastructure transitions from Arena toward Labyrinth as constraint density rises around verification, latency, and integration complexity. Institutional regulation occupies Fog — delayed response, high uncertainty, reactive enforcement. Market adoption occupies Arena with localized Trap conditions in narrow domains where machine execution already produces deterministic outcomes and human-in-the-loop alternatives have become uneconomic.
Dominant control mechanisms across the system run through feedback-loop closure rate (CC dominance at the decision and execution layers) and constraint-density escalation (FGR dominance at the security and verification layer). Equilibrium trajectory moves from open-loop behavior toward semi-closed loops in the near term, competing closed-loop systems in the medium term, and dominant closed-loop architectures with embedded verification and optimization in the long term.
Cross-Domain Dynamics
Control migrates toward actors that reduce feedback latency across decision, verification, and execution layers. AI agents accelerate decision cycles, blockchain enforces execution integrity, and quantum capabilities reshape optimization boundaries on the long-horizon clock. Adaptation is uneven across domains — technology evolves fastest, markets adopt selectively, capital reallocates on narrative before performance, and regulation lags until constraint violations force intervention.
Constraint geometry governs security and infrastructure outcomes. Post-quantum migration does not follow preference or strategy; migration follows inevitability once cryptographic vulnerability reaches a critical threshold. Institutions delay transition due to capital cost and legacy system inertia, but delay increases systemic risk and compresses the eventual migration window.
Strategic behavior across domains reflects delay-dominant equilibrium conditions. Incumbents preserve existing margins by slowing adoption, reframing risk, and leveraging regulatory latency. Startups exploit timing gaps by targeting forced-transition layers where demand is non-discretionary. Investors misallocate capital when treating convergence as simultaneous rather than staggered across three non-synchronized clocks.
Coordination across decentralized and centralized systems remains unstable. Protocol ecosystems fragment until incentive alignment improves. Agent identity, wallet control, and execution standards converge toward a smaller set of dominant architectures as coordination costs decline and network effects concentrate usage.
Domain-Level Dynamics
Capital markets. Capital reallocates unevenly because investors price a convergence story before underlying revenue clocks align. Agent infrastructure attracts near-term capital because monetization arrives first. Post-quantum migration attracts capital next because transition demand is forced rather than discretionary. Quantum compute absorbs speculative premium furthest ahead of commercial readiness. Pricing error narrows once revenue separation becomes visible, and the alpha transfer described in the Pricing Error section reverses.
Technology infrastructure. Providers compete to own verification, optimization, and latency compression rather than generic integration. Defensible advantage forms where firms control cryptographic trust, proprietary decision architecture, or execution speed that thinner competitors cannot match. Commodity orchestration layers lose pricing power as underlying capabilities open and standardize.
Institutional regulation. Regulators and standards bodies move on a slower clock than deployment markets. Response patterns begin with categorization error, proceed through selective intervention, and tighten only after visible security failures, market dislocation, or public coordination breakdown. Regulatory lag creates temporary arbitrage, but the window closes once forcing events convert optional adaptation into mandatory compliance.
Market adoption. Adoption begins in narrow environments where machine execution clearly lowers coordination cost — settlement, routing, identity, and other high-frequency decision domains. Broader adoption depends on trust standardization, wallet persistence, and reliable verification. User behavior shifts gradually at the surface and abruptly underneath once infrastructure friction falls below institutional alternatives.
Primary Simulation Predictions
Agent Execution Threshold. Agent-mediated transactions exceed a material share of machine-executable markets by end of 2027. Concrete threshold for falsification: agent-originated settlement below 15% of total on-chain transaction volume by that date invalidates the near-term convergence velocity assumption.
Post-Quantum Forcing Event. Post-quantum cryptographic migration accelerates sharply following a triggering event — a regulatory mandate or a high-profile security breach demonstrating harvest-now-decrypt-later exposure. Gradual transition without a discontinuity falsifies the constraint-dominance assumption and weakens the forced-adoption thesis.
Integration Margin Bifurcation. Integration layers split into two outcomes by 2029. System-level margin capture accrues to actors owning verification and optimization; margin compression toward zero occurs for actors relying on commodity orchestration. A unimodal margin distribution across integration firms falsifies the bifurcation prediction.
Feedback Dominance Advantage. Actors with lowest decision-to-execution latency outperform competitors even when underlying models or infrastructure are inferior. A consistent pattern of superior-model firms winning despite latency disadvantage falsifies the feedback-dominance prediction.
Secondary Monitoring Signals
Decline in human-in-the-loop transaction approval rates. Increase in autonomous agent identity persistence and wallet control. Acceleration of post-quantum standard adoption across financial and identity systems. Rising divergence between institutional narratives and observed behavior — particularly where public statements lag balance-sheet reallocation. Compression of coordination costs across blockchain-based execution environments. Increased clustering of regulatory interventions following latency spikes and visible failure events.
Simulation Falsification Conditions
Simulation-specific falsifiers extend the consolidated conditions in Section VI. Agent adoption stagnates below material thresholds by 2027. No significant acceleration in post-quantum migration following emerging risk signals. Integration layers retain uniform margin despite commoditization of underlying components. Regulatory systems adapt at parity with technological deployment speed. Failure to observe any of these invalidates core convergence assumptions and requires model recalibration rather than incremental adjustment.
Simulation Closing
Convergence reads as a control problem across interacting systems rather than a linear technology narrative. Outcomes depend on feedback latency, constraint thresholds, and institutional adaptation speed. Actors aligning across capital, infrastructure, regulation, and adoption capture durable advantage. Actors optimizing within a single domain without cross-domain integration lose position regardless of single-domain execution quality, because the system-level equilibrium punishes local optimization once feedback-loop closure rates separate winners from losers.
X. Named-Firm Positioning — Series Umbrella
Hyperscalers violate the startup-incumbent-investor taxonomy. Microsoft, Google, Amazon, Meta, and Oracle operate simultaneously as infrastructure providers, AI model owners, quantum hardware builders, venture investors through corporate venture arms, and — through self-funded capital expenditure projected at extraordinary scale in 2026 — as their own largest institutional investors. A hyperscaler’s control-and-power position resolves only by mapping each role separately against the three-clock framework.
Section X opens the Named-Firm Positioning series — an application layer to the governing framework developed in Sections I through IX. The first installment, below, provides a cross-sectional map of ten firms against the three-clock framework. Forthcoming installments under this umbrella:
Market Dynamics Installment — consolidation vectors, partnership topology, and revenue-clock divergence across the named-firm set. Tracks which firms move from capture point to capture point and at what rate.
Antitrust and Patent Installment — regulatory exposure, standards capture, and intellectual property positioning across the verification and optimization layers. Covers NIST post-quantum standards, NVQLink ecosystem governance, and antitrust exposure from vertical integration across the stack.
Investor Installment — portfolio construction against the three-clock framework with named-firm allocation logic by stage, horizon, and mandate. Covers venture concentration, public-equity directional trades, and long-cycle optionality sizing.
Firm-specific positioning is perishable. Balance-sheet commitments, roadmap claims, and quantum milestones can change faster than the governing structure. Readers should treat the section below as a dated application layer rather than a permanent ranking. Sections I through IX state the durable thesis; Section X applies it to a specific moment in 2026. Time sensitivity is a feature, not a flaw; divergence between framework and firm positioning is itself a signal.
The question is not which firm “wins” convergence outright; the question is which firms monetize the near clock, defend margin on the medium clock, and retain credible optionality on the long clock.
Named-Firm Set
The firms most capable of executing or blocking the convergence thesis also shape the current competitive map. Each operates a distinct multi-role profile across decision, verification, and feasibility, and each has already committed balance-sheet capital at a scale that sets the near-term pace of the convergence. Hyperscaler capital expenditure for the top five firms is projected to approach three-quarters of a trillion dollars in 2026, with roughly three-quarters directed to AI infrastructure. Self-investment at that scale makes these firms the convergence’s largest institutional investors in themselves.
Profiles below locate each firm against the three-clock framework and flag the specific capture points and failure modes relevant to that firm. Dates and metrics reflect publicly available 2025–2026 disclosures; readers should treat all quantum-timeline claims as roadmap targets rather than achieved milestones.
Microsoft
Role profile: cloud infrastructure provider (Azure), agent platform owner (Copilot and agent framework), quantum hardware bet (Majorana 1 topological qubit), and venture investor (M12, OpenAI stake). Microsoft is the only major firm pursuing topological qubits as its primary quantum architecture, which creates asymmetric upside if the approach scales and asymmetric downside if it does not.
Near-clock capture point: Azure as the primary commercial distribution channel for AI agent infrastructure, with agent persistence and wallet integration as the next monetizable layer.
Medium-clock capture point: post-quantum cryptographic migration across Azure services, enterprise identity (Entra), and Windows device attestation. Microsoft owns verification-layer positioning across enterprise better than any competitor.
Long-clock capture point: topological-qubit fault tolerance if the Majorana architecture delivers its four-generation roadmap on schedule. Independent replication of the 2025 Majorana results remains incomplete as of early 2026, and a July 2025 paper from Australian researchers raised decoherence-time challenges that Microsoft has publicly contested.
Failure mode: topological-qubit roadmap stalls while competitors reach fault tolerance via superconducting or trapped-ion paths, stranding Microsoft’s quantum optionality behind architectures it did not choose.
Google
Role profile: cloud infrastructure provider (Google Cloud), AI model owner (Gemini, DeepMind), quantum hardware builder (Willow superconducting chip, dual-track with neutral-atom research), and venture investor (GV, CapitalG). Google’s quantum positioning is more mature on the research side than Microsoft’s but equally distant from commercial deployment.
Near-clock capture point: Gemini agent infrastructure inside Workspace and consumer products. Google’s cold-start disadvantage in enterprise agent distribution compared to Microsoft is real but narrowing.
Medium-clock capture point: verification layer through combined attestation, identity (Google Identity), and Cloud KMS post-quantum primitives. Google has published more peer-reviewed quantum-error-correction work than any competitor.
Long-clock capture point: superconducting fault tolerance via Willow-successor architectures targeting commercial utility by end of the decade. Google’s October 2025 verifiable quantum advantage demonstration moved the firm meaningfully along its six-milestone roadmap.
Failure mode: Gemini distribution gap against Microsoft in enterprise closes too slowly while Google’s own AI spend compresses free cash flow. Capex at $175–185 billion for 2026 raises the bar for AI-revenue conversion inside the same window.
IBM
Role profile: enterprise services incumbent, AI model owner (Granite), quantum hardware leader (Heron, Nighthawk, Loon, Kookaburra roadmap toward Quantum Starling in 2029), and post-quantum cryptography standards participant. IBM is the only named firm whose public roadmap commits to fault-tolerant quantum computing at a specific date — 2029 — with 200 logical qubits and 100 million gate operations.
Near-clock capture point: quantum-classical hybrid services through Qiskit and IBM Quantum Network for enterprise exploration. Demand for quantum advantage demonstrations by end of 2026 drives commercial engagement ahead of fault tolerance.
Medium-clock capture point: post-quantum cryptographic migration across IBM’s enterprise install base — a captive customer set that must migrate and prefers a vendor already participating in the NIST standards process.
Long-clock capture point: first-mover fault-tolerant quantum deployment if the Starling roadmap executes. IBM’s willingness to publish a dated fault-tolerance commitment is itself a strategic posture; slippage damages credibility, execution establishes a hardware moat competitors would need years to close.
Failure mode: Starling timeline slips past 2029 while Google’s superconducting or Microsoft’s topological architectures reach scale first. IBM’s enterprise distribution advantage weakens if IBM arrives to fault tolerance second.
Amazon
Role profile: cloud infrastructure provider (AWS), AI model owner (Bedrock, Nova), quantum hardware bet (Ocelot cat-qubit chip through AWS Center for Quantum Computing at Caltech), quantum hardware aggregator (Braket multi-vendor platform), and venture investor. Amazon’s quantum capex pattern differs from Microsoft’s and Google’s — Amazon builds both proprietary hardware and a Switzerland-position marketplace for competitor hardware.
Near-clock capture point: Braket as the hardware-agnostic execution layer for enterprise quantum experimentation, capturing coordination rents regardless of which quantum architecture wins. Amazon’s $200 billion 2026 capex gives AWS the largest agent infrastructure buildout of any cloud.
Medium-clock capture point: AWS post-quantum migration, including partnerships with specialist firms (American Binary on Ambit Client). Amazon’s advantage is distribution breadth; post-quantum adoption on AWS forces adoption across its customer base.
Long-clock capture point: Ocelot’s cat-qubit architecture claims up to 90% reduction in physical qubits per logical qubit. If the claim holds at scale, Amazon reaches fault tolerance with materially lower capital intensity than superconducting or topological competitors.
Failure mode: Ocelot’s cat-qubit efficiency claim fails to replicate at scale, and Braket’s hardware-agnostic position becomes a commodity routing layer as fault-tolerant hardware consolidates.
Meta
Role profile: consumer platform owner (Facebook, Instagram, WhatsApp), AI model owner (Llama), AI infrastructure builder (1GW Ohio data center, Louisiana 5GW facility), and post-quantum cryptography co-developer (Meta cryptographers co-authored HQC, a NIST-selected PQC algorithm). Meta is not a quantum hardware bet and does not own cloud distribution, which sharpens focus on the two clocks where Meta can actually capture.
Near-clock capture point: Llama as the open-weight model underlying third-party agent infrastructure. Distribution through open weights is a different capture strategy than Microsoft’s or Google’s closed-platform model — Meta wins on ecosystem adoption rather than per-seat monetization.
Medium-clock capture point: post-quantum cryptographic migration across Meta’s production infrastructure, publicly framed around “store now, decrypt later” threat mitigation. Meta’s April 2026 migration framework publication puts the firm on record as a reference implementation for large-scale PQC rollout.
Long-clock capture point: limited. Meta has chosen not to build quantum hardware and relies on hyperscaler cloud access for any quantum-enhanced workloads.
Failure mode: open-weight distribution loses to closed-platform economics if agent infrastructure consolidates around Azure and Google Cloud, leaving Llama as a reference implementation rather than a monetization surface.
Apple
Role profile: device platform owner (iOS, macOS), identity provider (Apple ID, Apple Pay), AI model owner (Apple Intelligence), and post-quantum cryptography implementer (quantum-secure protocols in iOS 26, macOS 26, iPadOS 26 via hybrid classical-plus-PQC design). Apple’s convergence position is narrower and deeper than the hyperscalers’ — Apple owns the client endpoint for over a billion users.
Near-clock capture point: on-device agent infrastructure through Apple Intelligence, with privacy architecture as the differentiator against cloud-resident agents.
Medium-clock capture point: post-quantum cryptographic deployment at client scale. Apple’s hybrid deployment across iOS, macOS, and iPadOS represents the largest consumer PQC rollout and sets a client-side reference that enterprise cannot ignore.
Long-clock capture point: minimal direct exposure. Apple has not published a quantum hardware roadmap and relies on partners for any quantum compute dependency.
Failure mode: on-device agent infrastructure loses to cloud-resident agents if model capability advantages from hyperscaler infrastructure exceed Apple’s privacy and latency advantages.
Oracle
Role profile: enterprise database incumbent, cloud infrastructure provider (OCI), AI infrastructure partner (Stargate joint venture with OpenAI and SoftBank), and post-quantum cryptography deployment partner (American Binary Ambit Client on OCI, NIST Level 5 / CNSA 2.0 compliant). Oracle’s convergence position is narrower than the hyperscalers’ but its post-quantum federal positioning is unusually strong.
Near-clock capture point: AI infrastructure buildout through Stargate and OCI capacity for OpenAI workloads. Oracle’s $50 billion 2026 capex represents a 136% increase over 2025 against $523 billion in remaining performance obligations.
Medium-clock capture point: post-quantum deployment in federal and defense cloud — Oracle US Government Cloud, Oracle US Defense Cloud, Oracle National Security Regions. Federal PQC mandates favor vendors already in the compliance architecture.
Long-clock capture point: minimal. Oracle has not built quantum hardware.
Failure mode: Stargate execution risk. Oracle’s capex-to-revenue ratio reached 86% for 2026 — the highest of any hyperscaler — which compresses margin for error on infrastructure monetization timing.
Nvidia
Role profile: AI hardware monopolist (GPU), quantum-classical integration infrastructure provider (CUDA-Q, NVQLink, Ising open models), and ecosystem orchestrator. Nvidia has chosen not to build a quantum processing unit. The strategic position is explicitly infrastructure — the universal bridge between classical AI supercomputing and whichever quantum architectures reach commercial scale.
Near-clock capture point: GPU-accelerated decision and verification workloads across every AI agent deployment. Nvidia captures a tax on the entire AI stack regardless of which model or platform wins.
Medium-clock capture point: NVQLink as the interconnect standard between classical HPC and quantum processors. Nvidia’s April 2026 announcement specified 17 QPU builders, 5 controller builders, and 9 U.S. national labs on the NVQLink architecture. The Ising open-source AI models for quantum error correction extend the bridge further into the quantum stack.
Long-clock capture point: verification and optimization pathways through CUDA-Q compatibility with approximately 75% of quantum hardware platforms. Nvidia’s capture does not depend on which quantum architecture wins.
Failure mode: pick-and-shovel strategy fails if quantum vendors bypass NVQLink by building direct classical-coprocessor integration, or if hyperscalers route around Nvidia GPUs through custom silicon (Trainium, TPU) at sufficient scale.
IonQ
Role profile: quantum hardware pure-play (trapped-ion architecture), first public quantum firm to exceed $100 million in annual GAAP revenue ($130 million in 2025). IonQ guides $225–245 million for 2026 with $370 million in remaining performance obligations.
Near-clock capture point: enterprise quantum services revenue through QuantumBasel ($60 million four-year contract) and defense and networking contracts. Commercial traction ahead of most pure-play competitors.
Medium-clock capture point: 256-qubit system deployment on trapped-ion architecture with 99.99% two-qubit gate fidelity. IonQ’s architecture trades slower gate speeds for longer coherence times, a profile that suits some workloads and fails others.
Long-clock capture point: dependent on whether trapped-ion scales past the current technology frontier against superconducting and topological alternatives.
Failure mode: IonQ’s $22 billion valuation against $130 million in 2025 revenue makes the firm a target for multiple compression if the quantum-advantage narrative slows or if hyperscaler architectures deliver commercially useful quantum computing first.
Rigetti
Role profile: quantum hardware pure-play (superconducting architecture, chiplet-based scaling), with $589.8 million cash runway against $7.1 million 2025 revenue. Rigetti’s price-to-sales multiple exceeds 660x at current valuation — a multiple that only resolves through roadmap execution, not revenue growth within the current technology.
Near-clock capture point: 108-qubit Cepheus-1-108Q system deployment and Novera QPU on-premises sales to research institutions. Novera purchase orders of $5.7 million in Q1 2026 would approximately match full-year 2025 revenue.
Medium-clock capture point: 336-qubit system by late 2026 and 1,000-qubit chiplet architecture by end of 2027. Rigetti’s strategic partnerships with Quanta Computer, DARPA, and Nvidia provide funding and external validation.
Long-clock capture point: 4,000-plus qubit machine by 2029. Execution against this roadmap is the firm’s entire thesis.
Failure mode: revenue declined 34% in 2025 against rising capital needs and rising competition from hyperscaler-funded superconducting programs (Google Willow, Amazon Ocelot, IBM Heron/Nighthawk). Rigetti must hit its 336-qubit milestone on schedule while competing against firms whose quantum budgets exceed Rigetti’s total enterprise value.
Named-Firm Section Implication
No named firm holds durable advantage across all three clocks. Microsoft and Google cover near and medium clocks and hold a long-clock option. IBM covers all three but carries public roadmap risk. Amazon and Nvidia occupy structurally distinct positions — Amazon as hybrid builder-marketplace, Nvidia as universal bridge — that insulate against single-architecture failure but depend on substrate growth continuing. Meta, Apple, and Oracle cover fewer clocks but own deeper positions within their covered layers. IonQ and Rigetti carry the pure-play exposure: if quantum scales on their architectures, valuations justify; if hyperscalers reach fault tolerance first, valuations compress.
The strategic asymmetry investors and boards should price: every named firm has a credible near-clock or medium-clock capture, but long-clock fault tolerance remains a four-to-seven-firm race where the winner is unknown and the technology architectures are not substitutable. Portfolio construction across this named set should treat near-clock positions as the revenue base, medium-clock positions as the margin-defense layer, and long-clock positions as optionality sized to risk tolerance.
XI. Conclusion
Convergence across AI, quantum computing, and blockchain forms a new computational and economic substrate. Strategic focus shifts from individual technologies to integrated architectures — but only where the integration owns defensible assets, operates on an honest capability timeline, and compresses feedback latency below what vertically integrated competitors can match.
Dominance accrues to firms capturing the combined system, pricing each domain on its own clock, and surviving the falsification conditions that thinner theses cannot. Firms that misprice timelines, rely on substitutable integration, or fail to secure verification and optimization layers will lose margin even if convergence proceeds on schedule.
Markets will reward alignment across clocks and punish narrative that outruns execution.
Appendix. Foundational MindCast References
The frameworks deployed in this paper — Cognitive Digital Twin (CDT), Cybernetic Control (CC), Game Regime Identification (GRI), Strategic Game Theory (SGT), Field-Geometry Reasoning (FGR), Strategic Behavioral Coordination (SBC), Institutional Cognitive Plasticity (ICP), Installed Cognitive Grammar (ICG), Causation Vision (CV), Signal Suppression Equilibrium (SSE), and Double-Sided Rational Ignorance (DSRI) — were developed across prior MindCast publications. References below anchor the foundational and framework-specific lineage. Applied case studies (Compass Behavioral Economics Series, Kalshi / prediction markets corpus, Live Nation DOJ settlement validation, Consumer AI Device Series, Bellevue AI Series, and the CPI Antitrust Chronicle paper Infrastructure Routing Control) are catalogued separately at mindcast-ai.com.
1. MindCast Predictive Cybernetics Suite (umbrella). Three-installment runtime module unifying the full MindCast predictive cybernetics framework. Parent reference under which Predictive Institutional Cybernetics, Cybernetic Foundations, and Simulation Infrastructure operate as integrated components. Establishes the umbrella doctrine this paper applies to the AI × Quantum × Blockchain stack.
2. Predictive Institutional Cybernetics: How MindCast AI Uses Constraint Geometry, Runtime Geometry, and Causal Signal Integrity to Forecast Institutional Behavior. Runtime module documenting the CDT architecture, Vision Functions, and Causal Signal Integrity methodology. Foundational reference for the paper’s title and for the Cybernetic Control (CC) framework deployed in Section IX’s Foresight Simulation.
3. The Cybernetic Foundations of Predictive Institutional Intelligence: The Architecture of Institutional Foresight. Grounds MindCast’s methodology in the intellectual lineage running from Norbert Wiener and the Macy Conferences through Ashby’s Law of Requisite Variety, Beer’s Viable System Model, Bateson’s Learning II/III distinction, and Hayek’s information theory of markets. Theoretical substrate for the paper’s claim that convergence resolves into a control problem.
4. From Cybernetic Proof to Simulation Infrastructure. Develops the edge-domain validation argument — simulation systems prove architectural validity in compressed, fast-feedback environments before deployment in domains that matter. Methodological precedent for the Foresight Simulation output structure in Section IX, including the falsification-contract discipline applied to the paper’s predictions.
5. MindCast AI Constraint Geometry and Institutional Field Dynamics. Formalizes Constraint Geometry as a measurable architecture — constraint density, curvature steepness, institutional mass, topology redistribution, escape thresholds, and attractor stability — rather than metaphor. Direct foundation for the Field-Geometry Reasoning (FGR) framework cited in Section IX and for the constraint-density escalation mechanism governing post-quantum migration inevitability in Section IV.
6. Runtime Geometry, A Framework for Predictive Institutional Economics. Integrates Chicago School economics with Cognitive Digital Twin methodology to produce diagnostic architecture for institutional integrity. Four-pillar framework — Field-Geometry, Nash-Stigler Equilibrium, Tirole Advocacy Arbitrage, Systemic Externality Analysis — underlying the three-clock framework’s treatment of capital allocation, margin defense, and optionality as distinct structural bets.
7. MindCast AI Emergent Game Theory Frameworks: Defining NIBE and Strategic Behavioral Coordination. Unified doctrine for National Innovation Behavioral Economics (NIBE) and Strategic Behavioral Coordination (SBC), with formal statements, propositions, and departure claims from the existing literature. Foundational reference for the SBC module in Section IX and for the actor-class coordination logic in Section VII.
8. Prestige Markets as Signal Economies: A Model of Signal Suppression and Institutional Failure. Formalizes the Signal Suppression Equilibrium (SSE) framework — access dependence, reputational retaliation risk, information fragmentation, narrative distortion, and signal aggregation capacity — and the Signal Suppression Index (SSI) diagnostic. Direct foundation for the paper’s argument that narrative distortion suppresses early signals of convergence mispricing, that cascade-phase exposure follows extended suppression, and that divergence between framework and firm positioning is itself a signal — the core premise anchoring the Section X Series Umbrella.