MCAI Innovation Vision: The AI Infrastructure Energy Patent Landscape
AI Infrastructure Energy Series, Installment III Patents Compound Forward: How Incumbents Pre-Write the Constraint Field
The Power Stack — How Energy Infrastructure Became the New AI Battleground series navigation:
Installment I: The AI Infrastructure Energy Opportunity Landscape Capital Is Flowing to the Wrong AI Infrastructure Layer
Installment II: The AI Infrastructure Energy Antitrust Landscape When the Moats Become the Evidence
Installment III: The AI Infrastructure Energy Patent Landscape Patents Compound Forward: How Incumbents Pre-Write the Constraint Field (this publication)
Executive Summary
Competition in the preemption phase is not competition to build better systems. Competition in the preemption phase is competition to control the next design corridor.
Patents filed today against forced engineering trajectories will activate as binding constraints on entrants who have not yet reached scale. That is the operative claim of Installment III, and it is not a claim a patent attorney would make. A patent attorney sees the current constraint field. MindCast sees the dynamic: each generation of patent constraint shapes the engineering baseline that the next generation of patents will target. The constraint compounds forward, invisibly, before entrants experience it as exclusion.
AI infrastructure will not be decided by who builds the best systems, but by who controls the legal pathways that determine which systems are allowed to exist.
Thesis: The AI infrastructure patent system operates through Forward Constraint Compounding (FCC) — a proprietary MindCast AI analytical construct — in which each generation of constraint forces a trajectory that the next generation of patents pre-claims. Energy and deployment constraints force engineers onto narrow improvement trajectories. Incumbents observe those trajectories and file into them before entrants experience them as exclusion.
Installment III establishes patents as the missing control layer in the series. Installment I (The AI Infrastructure Energy Opportunity Landscape) showed where opportunity exists in the compute–power stack. Installment II (The AI Infrastructure Energy Antitrust Landscape) showed how antitrust reacts after concentration forms. Installment III explains why concentration forms in the first place: prior constraint geometry forces future improvement paths, and incumbents patent into those paths before entrants recognize the trap.
The series resolves into a causal chain: Patents (III) define feasible pathways. Opportunity (I) emerges within legally survivable corridors. Antitrust (II) reacts downstream after concentration has formed from constraint geometry. Without this ordering, concentration looks contingent. With it, concentration is predictable before it becomes visible.
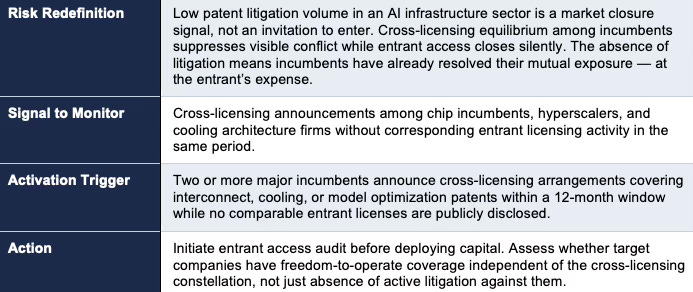
The Nash–Stigler interaction that governs this system produces a specific and non-obvious institutional failure. Nash equilibrium, here, describes how incumbent firms lock into stable cross-licensing arrangements with each other because mutual assertion would destroy everyone. Stigler equilibrium describes how regulatory and judicial institutions stop searching for problems once observable conflict levels appear low.
Together, these two dynamics produce a compounding failure: cross-licensing among incumbents suppresses visible litigation, and institutions read low litigation volume as system health. Entrant pathways close without triggering the signal that would produce correction. This is a proprietary MindCast AI synthesis framework; the full architecture is developed in Section IX. Enforcement will not be triggered by litigation volume. It will be triggered by an International Trade Commission (ITC) exclusion order — the mechanism that converts trajectory-based infringement into immediate, visible exclusion at the moment scaling reveals the constraint. P50 horizon: 24–36 months.
Series Positioning — Closing the Causal Loop
AI infrastructure operates as a cybernetic control system — a feedback architecture in which outputs from one layer regulate inputs to the next — linking compute demand, physical energy infrastructure, institutional governance, and capital allocation into a single self-reinforcing structure. Each installment isolates a layer. The series becomes predictive only when those layers are ordered correctly by causation.
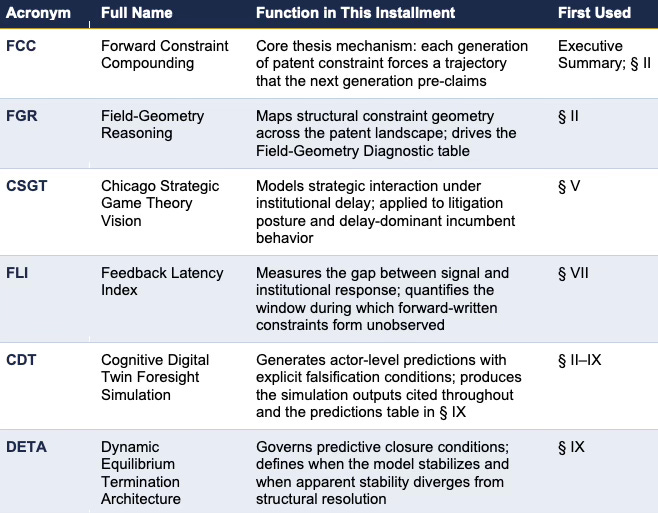
The following proprietary MindCast AI analytical frameworks are developed as part of the Predictive Institutional Cybernetics architecture and referenced throughout this installment. Full definitions appear in MindCast AI Economics Frameworks.
Installment I (The AI Infrastructure Energy Opportunity Landscape) mapped opportunity across the compute–power stack, identifying where constraint removal generates durable returns and where speculative capital accumulates positions without expanding system capacity. Installment II (The AI Infrastructure Energy Antitrust Landscape) documented how antitrust exposure accumulates at routing-layer control — and why the Becker-to-Posner transition from tolerated accumulation to actionable exclusion is predictable in timing. (Gary Becker’s framework treats regulatory outcomes as products of interest-group competition; Richard Posner’s extension operationalizes the point at which accumulation of market power crosses into legally cognizable exclusion. Both are Chicago School frameworks that MindCast deploys to time antitrust intervention.) Both installments take the structure of feasible competition as given. Installment III does not.
The constraint that determines which firms can compete, and on what terms, is set before Installments I and II become relevant. As established in How the U.S. Can Foster AI Innovation Using Intellectual Property as a National Innovation System (AI IP), legal feasibility precedes market structure. Forward Constraint Compounding (FCC) is the mechanism: incumbents patent into the forced trajectories that energy and physics create, before entrants experience those trajectories as exclusion. The series resolves into a single causal chain only when this upstream layer is in place.
Contact mcai@mindcast-ai.com to partner with us on Predictive AI in Law and Behavioral Economics. A full foresight simulation output report is available upon request.
To deep dive on MindCast work in Cybernetic Foresight Simulations upload the URL of this publication into any LLM and prompt ‘reconstruct MindCast framework with three degrees of cited sub links.’ See Live-Fire Game Theory Simulators, Runtime Predictive Infrastructure.
Recent projects: Chicago School Accelerated — AI Infrastructure Patent Coordination, Private Equity & Patent Litigation in AI Data Centers (2026–2028), Quantum Computing Sovereignty — How Patent Ecosystems Will Shape the Future of Quantum-AI Data Centers.
I. Core Insight — Patents as Runtime Control
Patents function as runtime control layers that regulate who can execute within the AI infrastructure system. Legal rights do not sit passively on paper. They activate as permission gates that determine whether specific architectures can be deployed at scale — and under FCC, they activate against a trajectory the incumbent already mapped, at a moment the entrant cannot anticipate.
The runtime framing extends the thesis in AI Infrastructure IP (AI IP), which treats intellectual property as an active control surface rather than a passive asset class. Permission gates span critical layers of the stack: chip architecture, interconnect design, data center cooling and power distribution, and model optimization pipelines. Each layer introduces a boundary condition that restricts feasible system design independently. Those restrictions compound across layers for any actor attempting to assemble a full-stack deployment. FCC adds a temporal dimension to that compounding: gates are not simply present or absent, they are being written against the paths that entrants have not yet reached.
Control of permission gates under FCC therefore produces a structurally different competitive advantage than conventional patent blocking. Incumbents do not merely prevent copying. They pre-occupy the destination.
II. Field Geometry of the Patent Stack
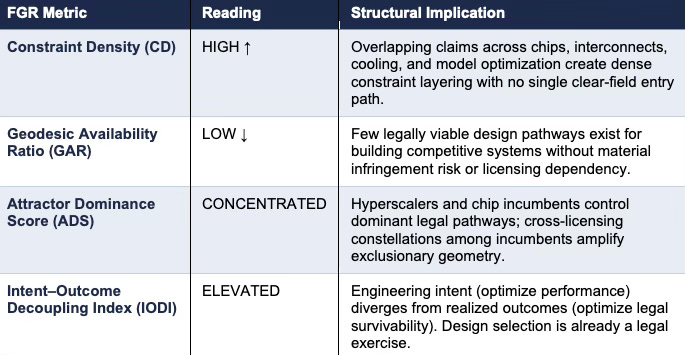
The patent landscape exhibits structural curvature that overrides intent and incentives. Field-Geometry Reasoning (FGR) identifies high constraint density, limited geodesic availability, and dominant attractors concentrated among hyperscalers and chip incumbents. Empirical patterns described in AI Infrastructure IP (AI IP) and Chicago School Accelerated — AI Infrastructure Patent Coordination show that innovation pathways are increasingly selected for legal survivability. Engineers select designs that minimize litigation exposure rather than maximize performance. Legal survivability becomes the governing constraint shaping technical evolution.
Field-Geometry Diagnostic — AI Infrastructure Patent Field
If CD continues rising and GAR continues falling through 2027, independent AI infrastructure entrants will cluster into licensing-dependent architectures rather than standalone systems.
Energy–Compute Coupling and Design Space Compression
AI infrastructure imposes constraints that do not exist in most software domains. Compute scaling requires extreme power density, thermal management, and grid integration. Chip design, interconnect architecture, cooling systems, and power distribution operate as a coupled system rather than independent layers. Architectures must satisfy simultaneous requirements of energy stability, thermal reliability, and legal feasibility. Designs that fail any dimension do not scale and therefore do not enter the reference set engineers iterate on.
Coupling increases constraint density and reduces viable design pathways. Reference architectures in AI infrastructure are not only legally survivable but physically proven under extreme energy conditions. Innovation compresses toward incremental improvements on these coupled systems rather than exploration of alternative designs.
The Installed Reference Architecture — The Hidden Constraint
Patent systems do not directly instruct engineers what to build. Patent systems determine which architectures survive long enough to become the baseline for improvement. That survival filter is FCC’s first stage: it produces the reference architecture that both incumbents and entrants must optimize against.
Engineers optimize against what exists. Existing systems reflect prior legal feasibility. Designs that cannot survive patent constraints do not scale, do not standardize, and do not enter the reference set engineers use for iteration. The hidden constraint is not visible in the reference architecture itself — it has already been resolved before that architecture became the reference. What remains is the product of filtering, not the filter. CDT simulation output: Reference Lock Score (RLS): HIGH. The installed reference architecture is not a starting point that competition can displace — it is a constraint that competition must accept.
Patents determine the architectures that survive. Surviving architectures determine what engineers optimize. The constraint does not appear in engineering plans; it has already been resolved before planning begins.
Empirical Anchor — GPU Stack (Compute + Interconnect)
Modern AI workloads converge on GPU-centric architectures anchored by CUDA-based software stacks and high-bandwidth interconnect systems. Developers optimize against this environment because it is the only architecture that has demonstrated scalable performance under real-world deployment conditions.
Alternative compute paradigms face a compound barrier: they must match performance, integrate with existing software ecosystems, and avoid infringement across interconnect, memory coordination, and parallelization techniques. Alternative architectures attempting looser coupling or different memory coordination failed to meet synchronization and bandwidth requirements at scale, and therefore never entered production systems where they could establish a competing reference baseline. Dominant attractors emerge not because alternatives are inconceivable, but because alternatives fail to survive the combined constraints of performance, ecosystem lock-in, and legal exposure.
Empirical Anchor — Data Center Cooling and Power Architecture
AI data centers operate under extreme power density and thermal load, requiring tightly integrated cooling and power distribution systems. Liquid cooling, immersion techniques, and rack-level thermal management designs represent a narrow set of architectures that have proven viable at scale. Each embeds patented methods across fluid dynamics, heat exchange, and power routing. New designs must satisfy thermal stability, grid compatibility, and legal clearance simultaneously. Designs that fail any constraint do not deploy and do not become part of the engineering reference set.
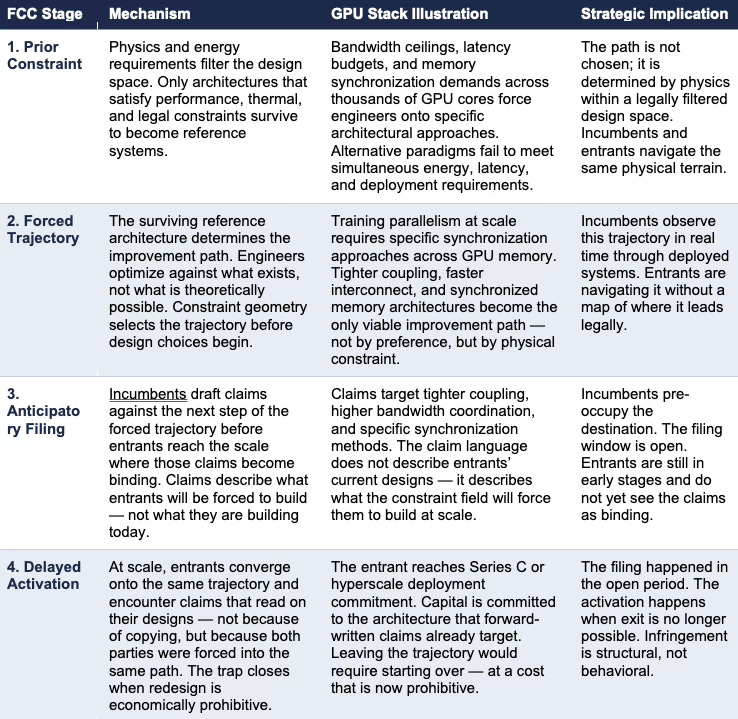
Worked Example — The Forward-Compounding Mechanism
This is Forward Constraint Compounding (FCC) in operation: constraint → forced trajectory → anticipatory filing → delayed activation at scale. Each generation of patent constraint shapes the engineering baseline that the next generation of patents will target. The entrant does not encounter yesterday’s claims. It encounters tomorrow’s, already written against the path physics made inevitable.
III. Chicago Accelerated — Preemption Dynamics
Patent behavior in AI infrastructure follows a three-phase acceleration pattern that transforms protection into preemption, as formalized in Chicago Accelerated Patents. Initial coverage expands filings across adjacent domains. Interlock creates cross-layer dependencies. Preemption establishes overlapping claims that block competing architectures.
Preemption in AI infrastructure operates on a forward-written basis. The installed reference architecture reveals where engineers must go next. Patent strategy targets that path before it becomes visible as competition. CDT simulation outputs: Forward Filing Index (FFI): HIGH; Claim Target Specificity (CTS): INCREASING. Claims are not broadening speculatively — they are narrowing precisely, drafted against the forced trajectory with increasing specificity as that trajectory becomes more legible through deployed systems. The strategic implication is asymmetric: incumbents operate with a map of the forced trajectory; entrants navigate it without one.
The system has entered the preemption phase. Patent portfolios now define exclusion zones where entry is legally prohibited, licensing corridors where participation requires payment, and litigation triggers that activate upon scale. The relevant competitive question is no longer which firm builds the best system — it is which firm controls the corridor the next system must traverse.
IV. Runtime Causation — Late Activation of Patent Power
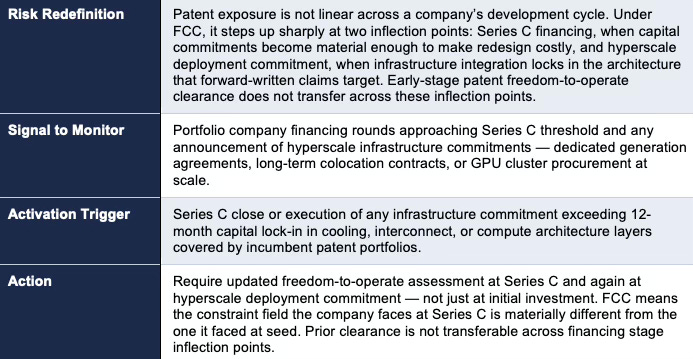
Patent control activates at the scaling phase, not during early innovation. The dynamic is temporal displacement of control: patents bind not the exploration phase, but the improvement trajectory that follows it. During early experimentation, the system appears open. Patent claims filed against the forced trajectory do not yet bind anyone, because no one has yet reached the scale where the trajectory becomes obligatory.
The asymmetry is structural. Incumbents drafting anticipatory claims know the trajectory is closed; they filed against it. Entrants navigating that trajectory do not know it is closed until scale reveals the constraint. CDT simulation outputs: Activation Delay Window: 12–36 months; Scale Trigger Threshold: Series C financing or hyperscale deployment commitment. Both mark the point at which capital becomes irreversible and redesign becomes economically prohibitive. The filing happens in the open period. The activation happens when exit is no longer possible.
The design-around trap is FCC’s sharpest implication, and the one most likely to be missed by conventional IP analysis. An entrant that successfully avoids current patent claims has not escaped the constraint field. It has optimized more precisely into the forced trajectory, positioning itself closer to the next claim generation’s coverage envelope. Design-around success narrows the entrant’s design space further, because it eliminates the paths already known to be legally exposed and leaves only the paths incumbents have already identified as the forced trajectory’s next step. The conventional IP response — design around the claims — accelerates capture rather than preventing it. The entrant solving yesterday’s claim is being steered into tomorrow’s.
The capital–IP convergence documented in MCAI Market Vision: Private Equity & Patent Litigation in AI Data Centers (2026–2028) reflects this timing: PE firms executing infrastructure roll-ups are accumulating patent exposure at the same rate they accumulate megawatts. Freedom-to-operate opinions and defensive portfolio acquisitions are becoming standard deal components because the runtime causation timing is now widely enough understood that capital actors are pricing it — even if they cannot yet name the mechanism.
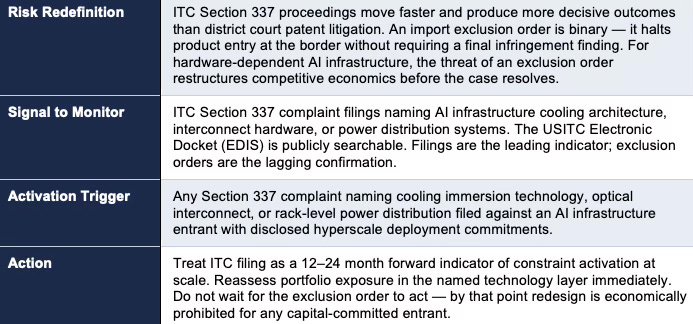
V. Patent Litigation Geometry
Strategic interaction in patent environments prioritizes delay over immediate resolution. Under FCC, litigation posture shifts in a specific and non-obvious way: patent holders asserting forward-written claims do not need to prove copying. They need only show that the entrant converged onto the anticipated trajectory — which the constraint field made inevitable. CDT simulation output: Convergence Infringement Likelihood: HIGH. In a forward-compounding system, infringement risk becomes a function of trajectory alignment rather than copying behavior. Convergence is the evidence; the physics did the rest.
Findings in PE Litigation map directly onto Chicago Strategic Game Theory Vision (CSGT) outputs: high strategic delay preference, rule mutability, and persistent equilibria under loss. Litigation functions as a temporal control mechanism. Dominant actors extend timelines through jurisdictional fragmentation, discovery expansion, and procedural maneuvering. Time becomes the scarce resource that weaker actors cannot sustain.
Delay amplifies the forward-written constraint. Entrants reach scale and encounter claims already aligned with their design path. Delay increases settlement pressure because redesign — the only alternative to licensing — would require leaving the constrained trajectory entirely, at a cost that is often prohibitive after capital has committed to the existing architecture. Legal victory is not required; survival through the timeline determines outcome.
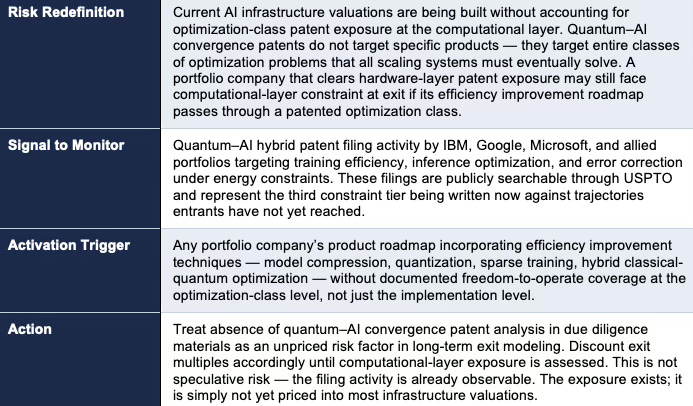
VI. Quantum and AI Patent Convergence
Patent scope is expanding from discrete inventions to classes of computation, as detailed in Quantum Computing Sovereignty — How Patent Ecosystems Will Shape the Future of Quantum-AI Data Centers. Under FCC, this expansion does not merely add a new constraint layer. It targets the trajectory itself — not products but entire future improvement paths. At the computational layer, the forced trajectory is not a specific architecture but a class of optimization problems that all scaling systems must solve. Every AI system operating under energy and compute constraints will eventually require efficiency improvements in training, inference, and error correction. Patents targeting those optimization classes pre-claim the destination before any specific system arrives there.
A claim covering an optimization class — such as training efficiency under constrained energy budgets, or error correction under thermal noise conditions — does not block one model or one architecture. It blocks all architectures that must pass through that optimization pathway as they improve. The forward-written mechanism scales upward: patents are drafted against inevitable classes of improvement, not isolated implementations.
Constraint density therefore compounds faster at the computational layer than at the hardware layer. Entire design directions become legally inaccessible without licensing — not because any specific implementation is covered, but because the approach category is covered. The Geodesic Availability Ratio, already LOW at the product level, compresses further when computational-level claims are aggregated with conventional portfolio positions.
MindCast’s Quantum Computing Sovereignty analysis predicts that by 2028 compute access will hinge on three currencies: patent sovereignty, trade-secret trust, and pipeline continuity. Installment III integrates that prediction into the series: quantum–AI convergence patents add a third constraint tier above the chip and energy infrastructure layers analyzed in Installments I and II. Capital allocators positioning in AI infrastructure without accounting for this convergence layer are pricing incomplete risk.
VII. Feedback Latency Window
Institutional response lags behind technological and legal development. Under FCC, this latency has a specific and asymmetric effect: the next constraint field is written before institutions observe exclusion. The system appears open not because constraints are absent, but because enforcement has not yet made them observable. Entrants interpret absence of enforcement as absence of constraint. Both conditions look identical from the outside during the filing window.
Elevated feedback latency across courts, patent offices, and regulatory systems creates a window where forced trajectories are being patented but not yet enforced. CDT simulation output: Enforcement Visibility Lag (Feedback Latency Index): HIGH. As highlighted in PE Litigation, delay functions as both shield and weapon — shielding incumbents who have filed into the trajectory, weaponizing time against entrants who cannot sustain the carrying cost of multi-year proceedings once scale has committed their capital. The window is structurally limited.
The relevant horizon is 12–36 months. During that window, incumbents file into forced trajectories. After the window closes, those filings activate at scale and constraint geometry becomes visible only after it has already bound the system. Positions established before latency compresses — licensing architecture, freedom-to-operate coverage, portfolio acquisitions at pre-assertion valuations — will be structurally more favorable than equivalent positions negotiated after enforcement has clarified the constraint field.
The most consequential infrastructure decisions in AI are not the ones made after the market is understood. They are the ones made during the latency window, when the constraint field is forming and enforcement has not yet activated. That window does not announce its closure.
VIII. Institutional Limits — Antitrust Lag
Antitrust frameworks operate downstream of the mechanisms that determine feasibility. Under FCC, this creates a structural mismatch that cannot be corrected by faster enforcement alone: antitrust measures exclusion at the point of market outcome, while forward-compounding patents determine exclusion at the point of trajectory formation. By the time antitrust observes pricing or market share effects, entrants have already been forced onto trajectories that are legally pre-claimed. The constraint was embedded before the market formed.
The upstream constraint dynamic is central to AI Infrastructure IP (AI IP): legal feasibility precedes market structure. That upstream gap is not a lag that faster enforcement can close — cross-licensing suppresses the conflict signal that would trigger enforcement in the first place, producing Signal Suppression Equilibrium (SSE) — a proprietary MindCast AI framework describing the condition where incumbent cross-licensing removes the visible conflict that institutions use as a health signal, causing enforcement to stand down even as entrant access closes — at the institutional layer before antitrust has registered that access has closed. By the time antitrust intervenes, patent geometry has already constrained who can participate.
Forward-written preemption produces a specific institutional failure that distinguishes this analysis from Installment II’s antitrust framing: cross-licensing among incumbents reduces visible litigation. Institutions read low litigation volume as system health. The underlying geometry — incumbents cross-licensing to mutual stability while entrant pathways close silently — is invisible to actors monitoring conflict rather than access. Legal systems designed to correct market outcomes cannot reverse constraints embedded before competition begins.
IX. Foresight Simulation — Patent-Control Equilibrium
Cybernetic Architecture
Cognitive Digital Twin (CDT) foresight simulation maps the AI infrastructure patent system stabilizing through three interacting feedback loops. Patent constraints define the signal boundary, establishing which actions are permissible (cybernetic control layer). Strategic actors adapt within those constraints, selecting architectures and licensing positions that optimize outcomes given the constraint field (Nash equilibrium layer). Institutional actors update doctrine until they reach perceived sufficiency — the state where further search appears unnecessary given existing rules (Stigler equilibrium layer).
Nash–Stigler Interaction — The Signal Suppression Equilibrium Failure Mode
Where Nash equilibrium governs incumbent behavior (stable mutual non-assertion through cross-licensing) and Stigler equilibrium governs institutional behavior (enforcement standdown when conflict metrics look healthy), their combination produces a failure mode that neither framework predicts alone. The cross-licensing equilibrium among AI infrastructure incumbents is stable among those parties precisely because assertion against each other produces mutual destruction at a cost neither can absorb. That stability is not neutral. It is exclusionary toward entrants who have no portfolio to contribute to the constellation and therefore cannot access the cross-license terms that make participation viable for incumbents.
The Stigler equilibrium layer is where the non-obvious institutional failure emerges. Institutional actors — USPTO, PTAB, courts, standard-setting bodies — measure patent system health by observable conflict. Cross-licensing among incumbents reduces observable conflict. Low conflict reads as stability. Institutions cease active search for systemic problems. Enforcement attention relaxes.
The result is Signal Suppression Equilibrium (SSE) — a proprietary MindCast AI framework — applied to the patent layer: the absence of visible conflict among incumbents suppresses the institutional signal that would otherwise trigger correction, even as entrant access closes silently. The system is in equilibrium. The equilibrium is exclusionary. Institutions have stopped searching because the metric they monitor looks healthy.
Forcing Event Prediction
Enforcement intervention will not be triggered by litigation volume — that signal is structurally suppressed by cross-licensing equilibrium. Intervention will be triggered by an entrant forcing event that makes exclusion visible to an institutional actor that had previously registered the system as stable.
The ITC complaint path is the most analytically grounded first trigger. ITC proceedings move faster than district court litigation. The remedy — an import exclusion order — is binary and immediate rather than retrospective damages. Infrastructure investment stakes are high enough that an exclusion order on cooling architecture or interconnect hardware makes the constraint geometry visible in a way no damages award can replicate. Critically, the ITC path aligns structurally with FCC: it converts trajectory-based infringement into immediate exclusion at the moment scaling reveals the constraint. The forward-written mechanism and the ITC remedy arrive at the same inflection point from opposite directions.
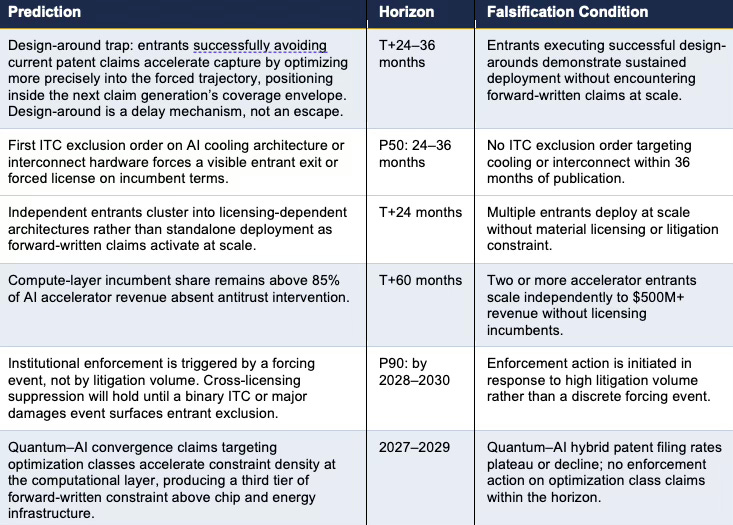
CDT Foresight Predictions — Falsifiable, Timestamped
Dynamic Equilibrium Termination Architecture (DETA) Termination Condition: Predictive closure occurs when (i) Nash equilibrium stabilizes incumbent behavior through cross-licensing and (ii) Stigler equilibrium suppresses institutional search due to low observed conflict. The system will appear stable before it has produced durable efficient outcomes. Apparent stability and structural resolution are not the same condition. The distinction between them is the operative analytical challenge for the next 24–36 months.
Falsification Hook: The model is falsified if entrants scale without encountering forward-written patent constraints, or if institutional intervention is triggered absent a discrete forcing event — that is, if litigation volume alone proves sufficient to activate correction.
X. Investor Brief — Four Decision Nodes for Capital Allocators
The analytical sections of this document establish the mechanism. This section converts that mechanism into four decision nodes for family office investors, corporate risk managers, and strategic planning teams. Each node identifies a specific observable signal, the trigger that confirms the risk is activating, and the action it implies. FCC does not produce diffuse background risk — it produces concentrated, predictable inflection points. The value is in knowing which ones to watch and what to do when they appear.
Decision Node 1 — The Litigation Inversion
Decision Node 2 — ITC Docket as Forward Indicator
Decision Node 3 — Financing Stage as Patent Risk Inflection
Decision Node 4 — Quantum Convergence as Unpriced Exit Risk
The analytical sections of this document establish why the AI infrastructure patent market is structurally exclusionary. This brief establishes what to do about it. The four decision nodes above are not predictions — they are monitoring protocols derived from the FCC mechanism. Capital allocators who implement them will see the constraint field before it activates. Those who do not will see it after.